vulnerability assessment
1 vulnerability assessment
2 vulnerability assessment
3 vulnerability assessment
4 vulnerability assessment
См. также в других словарях:
Vulnerability assessment — A vulnerability assessment is the process of identifying, quantifying, and prioritizing (or ranking) the vulnerabilities in a system. Examples of systems for which vulnerability assessments are performed for include, but are not limited to,… … Wikipedia
vulnerability assessment — A Department of Defense, command, or unit level evaluation (assessment) to determine the vulnerability of a terrorist attack against an installation, unit, exercise, port, ship, residence, facility, or other site. Identifies areas of improvement… … Military dictionary
Retina Vulnerability Assessment Scanner — is a vulnerability scanner created by eEye Digital Security that remotely scans a network for security vulnerabilities and assigns a level of threat to those discovered. It is only intended for corporate or government use. Purchase or evaluation… … Wikipedia
OpenSource Vulnerability Assessment Scanner — OpenVAS OpenVAS Développeur Intevation GMBH Dernière version … Wikipédia en Français
Open source Vulnerability Assessment Scanner — OpenVAS OpenVAS Développeur Intevation GMBH Dernière version … Wikipédia en Français
nuclear vulnerability assessment — branduolinio poveikio įvertinimas statusas T sritis apsauga nuo naikinimo priemonių apibrėžtis Galimo branduolinio smūgio prognozuojamo poveikio gyventojams, kariuomenei ir ištekliams įvertinimas. Jis pirmiausia atliekamas prieš smūgį; tačiau… … Apsaugos nuo naikinimo priemonių enciklopedinis žodynas
nuclear vulnerability assessment — branduolinio poveikio įvertinimas statusas T sritis Gynyba apibrėžtis Branduolinio ginklo naudojimo galimų padarinių gyventojams, pajėgoms ir ištekliams įvertinimas. Dažniausiai atliekamas prieš puolimą, tačiau gali būti pratęstas puolimo ar… … NATO terminų aiškinamasis žodynas
nuclear vulnerability assessment — The estimation of the probable effect on population, forces, and resources from a hypothetical nuclear attack. It is performed predominantly in the preattack period; however, it may be extended to the transattack or postattack periods … Military dictionary
threat and vulnerability assessment — In antiterrorism, the pairing of a facility … Military dictionary
Social vulnerability — Research on social vulnerability to date has stemmed from a variety of fields in the natural and social sciences. Each field has defined the concept differently, manifest in a host of definitions and approaches (Blaikie, Cannon et al. 1994;… … Wikipedia
What is Vulnerability Assessment? Testing Process, VAPT Scan Tool
Updated October 8, 2021
Vulnerability Testing
Vulnerability Testing also called Vulnerability Assessment is a process of evaluating security risks in software systems to reduce the probability of threats. The purpose of vulnerability testing is reducing the possibility for intruders/hackers to get unauthorized access of systems. It depends on the mechanism named Vulnerability Assessment and Penetration Testing(VAPT) or VAPT testing.
A vulnerability is any mistake or weakness in the system’s security procedures, design, implementation or any internal control that may result in the violation of the system’s security policy.
In this tutorial, you will learn-
Why do Vulnerability Assessment
Vulnerability Assessment Process
Here is the step by step Vulnerability Assessment Process to identify the system vulnerabilities.
Step 1) Goals & Objectives : – Define goals and objectives of Vulnerability Analysis.
Step 2) Scope : – While performing the Assessment and Test, Scope of the Assignment needs to be clearly defined.
The following are the three possible scopes that exist:
Step 3) Information Gathering : – Obtaining as much information about IT environment such as Networks, IP Address, Operating System Version, etc. It’s applicable to all the three types of Scopes such as Black Box Testing, Grey Box Testing and White Box Testing.
Step 4) Vulnerability Detection : – In this process, vulnerability scanners are used to scan the IT environment and identify the vulnerabilities.
Step 5) Information Analysis and Planning : – It will analyze the identified vulnerabilities to devise a plan for penetrating into the network and systems.
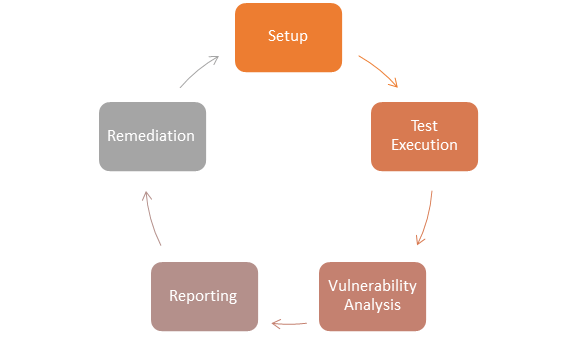
How to do Vulnerability Assessment
Following is the step by step process on How to do Vulnerability Assessment :
Step 1) Setup:
Step 2) Test Execution:
Step 3) Vulnerability Analysis:
Step 4) Reporting
Step 5) Remediation:
Types of a vulnerability scanner
Tools for Vulnerability Scanning
1) Acunetix
Features:
2) Intruder
Intruder is a powerful online vulnerability scanner that discovers security weaknesses across your IT environment. Offering industry-leading security checks, continuous monitoring and an easy-to-use platform, Intruder keeps businesses of all sizes safe from hackers.
Features:
| Category | Tool | Description |
|---|---|---|
| Host Based | STAT | Scan multiple systems in the network. |
| TARA | Tiger Analytical Research Assistant. | |
| Cain & Abel | Recover password by sniffing network, cracking HTTP password. | |
| Metasploit | Open source platform for developing, testing and exploit code. | |
| Network-Based | Cisco Secure Scanner | Diagnose and Repair Security Problems. |
| Wireshark | Open Source Network Protocol Analyzer for Linux and Windows. | |
| Nmap | Free Open Source utility for security auditing. | |
| Nessus | Agentless auditing, Reporting and patch management integration. | |
| Database-Based | SQL diet | Dictionary Attack tool door for SQL server. |
| Secure Auditor | Enable user to perform enumeration, scanning, auditing, and penetration testing and forensic on OS. | |
| DB-scan | Detection of Trojan of a database, detecting hidden Trojan by baseline scanning. |
Advantages of Vulnerability Assessment
Disadvantages of Vulnerability Assessment
Comparison of Vulnerability Assessment and Penetration Testing
| Vulnerability Assessment | Penetration Testing | |
|---|---|---|
| Working | Discover Vulnerabilities | Identify and Exploit Vulnerabilities |
| Mechanism | Discovery & Scanning | Simulation |
| Focus | Breadth over Depth | Depth over Breadth |
| Coverage of Completeness | High | Low |
| Cost | Low- Moderate | High |
| Performed By | In-house Staff | An attacker or Pen Tester |
| Tester Knowledge | High | Low |
| How often to Run | After each equipment is loaded | Once in a year |
| Result | Provide Partial Details about Vulnerabilities | Provide Complete Details of Vulnerabilities |
Vulnerability Testing Methods
Active Testing
Passive Testing
Network Testing
Distributed Testing
Conclusion
In Software Engineering, Vulnerability Testing depends upon two mechanisms namely Vulnerability Assessment and Penetration Testing. Both these tests differ from each other in strength and tasks that they perform. However, to achieve a comprehensive report on Vulnerability Testing, the combination of both procedures is recommended.
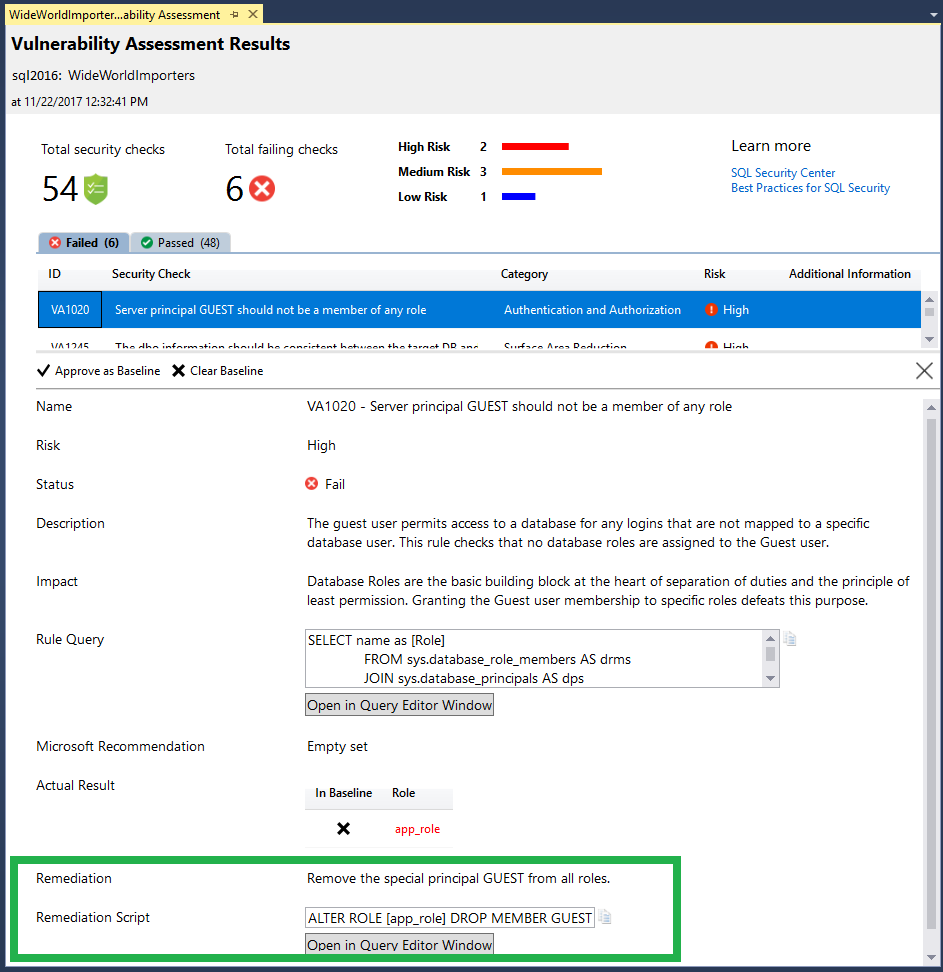
Vulnerability assessment for SQL Server
SQL vulnerability assessment is an easy to use tool that can help you discover, track, and remediate potential database vulnerabilities. Use it to proactively improve your database security.
The vulnerability assessment tool is available in SQL Server Management Studio (SSMS) for SQL Server 2012 or later.
For a comprehensive solution with advanced threat protection capabilities, use Microsoft Defender for SQL Servers on machines. To use this Microsoft Defender plan, your SQL Server must be connected to Azure.
For Azure SQL Database, Azure Synapse Analytics, and SQL Managed Instance, use Microsoft Defender for SQL Database.
Vulnerability assessment features
SQL vulnerability assessment (VA) is a service that provides visibility into your security state, and includes actionable steps to resolve security issues and enhance your database security. It can help you:
The VA service runs a scan directly on your database. The service employs a knowledge base of rules that flag security vulnerabilities and highlight deviations from best practices, such as misconfigurations, excessive permissions, and unprotected sensitive data. The rules are based on Microsoft’s recommended best practices, and focus on the security issues that present the biggest risks to your database and its valuable data. These rules also represent many of the requirements from various regulatory bodies to meet their compliance standards.
Results of the scan include actionable steps to resolve each issue and provide customized remediation scripts where applicable. An assessment report can be customized for your environment, by setting an acceptable baseline for permission configurations, feature configurations and database settings.
Prerequisites
This feature is only available on SQL Server Management Studio (SSMS) v17.4 or later. You can find the latest version here.
Getting started
To run a vulnerability scan on your database, follow these steps:
Open SQL Server Management Studio.
Connect to an instance of the SQL Server Database Engine or localhost.
Expand Databases, right-click a database, point to Tasks, select Vulnerability assessment, and select Scan for Vulnerabilities.
You can run a scan that checks for server-level issues by scanning one of the system databases. Expand System Databases, right-click the master database, point to Tasks, select Vulnerability Assessment, and click on Scan for Vulnerabilities.
Tutorial
Use the following steps to run and manage vulnerability assessments on your databases.
1. Run a scan
The Scan For Vulnerabilities dialog allows you to specify the location where scans will be saved. You can leave the default location or click Browse. to save the scan results to a different location.
When you are ready to scan, select OK to scan your database for vulnerabilities.
The scan is lightweight and safe. It takes a few seconds to run, and is entirely read-only. It does not make any changes to your database.
2. View the report
When your scan is complete, your scan report is automatically displayed in the primary SSMS pane. The report presents an overview of your security state; how many issues were found, and their respective severities. Results include warnings on deviations from best practices, as well as a snapshot of your security-related settings, such as database principals and roles and their associated permissions. The scan report also provides a map of sensitive data discovered in your database, and includes recommendations of the built-in methods available to protect it.
3. Analyze the results and resolve issues
Review your results and determine which findings in the report are true security issues in your environment. Drill-down to each failed result to understand the impact of the finding, and why each security check failed. Use the actionable remediation information provided by the report to resolve the issue.
4. Set your Baseline
As you review your assessment results, you can mark specific results as being an acceptable Baseline in your environment. The baseline is essentially a customization of how the results are reported. Results that match the baseline are considered as passing in subsequent scans.
Once you have established your baseline security state, VA only reports on deviations from the baseline, and you can focus your attention on the relevant issues.
5. Run a new scan to see your customized tracking report
After you complete setting up your Rule Baselines, run a new scan to view the customized report. VA now reports only failing security issues that deviate from your approved baseline state.
6. Open a previously run scan
You can also open an existing scan result via the File->Open menu. Select Vulnerability Assessment. and open the scans directory to find the scan result you wish to view.
VA can now be used to monitor that your databases maintain a high level of security at all times, and that your organizational policies are met. If compliance reports are required, VA reports can be helpful to facilitate the compliance process.
Manage vulnerability assessments using PowerShell
You can use PowerShell cmdlets to programmatically manage vulnerability assessments for your SQL Servers. The cmdlets can be used to run assessments programmatically, export the results and manage baselines. To get started, download the latest SqlServer PowerShell module from the PowerShell Gallery site. You can learn more here.
Next steps
Learn more about SQL vulnerability assessment using the following resources:
Vulnerability Assessment
What Is Vulnerability Assessment?
Vulnerability assessment is an evaluation method that enables organizations to review their systems for potential security weaknesses. It performs a vulnerability analysis process that aims to discover whether the organization is at risk of known vulnerabilities, assigns a level of severity to those vulnerabilities, and recommends whether a threat should be mitigated or remediated.
Vulnerability testing helps organizations discover whether their systems and software have active default settings that are insecure, which can include easily guessable admin passwords. It also assesses vulnerability to code injection attacks, such as Structured Query Language injection (SQLi) and cross-site scripting (XSS) attacks, and checks for a potential escalation of user privileges or incorrect authentication mechanisms.
Types of Vulnerability Assessments
The most common types of vulnerability assessments that organizations deploy are:
4 Steps of Vulnerability Assessment
Organizations that undergo a vulnerability assessment will follow a four-step process.
However, it is important to remember that a vulnerability assessment is not a one-off activity that organizations forget about when it has been completed. It must be repeated regularly and operationalized by encouraging development, security, and operations teams to cooperate closely with each other—a process called DevSecOps.
Vulnerability Identification
The first step is to create a comprehensive list of vulnerabilities in an organization’s applications, servers, and systems. This is done by either scanning them using specific internet vulnerability assessment tools or by testing them manually. Vulnerability analysts can also use vulnerability databases, vendor announcements, threat intelligence feeds, and asset management systems to identify potential weaknesses.
This first step of the process helps organizations understand the full details. This includes elements like risk appetite and tolerance level, business impact analysis, mitigation practices and policies, countermeasures for devices and services, and residual risk treatment.
Vulnerability Analysis
The second step aims to discover the source and initial cause of the vulnerabilities identified in the first step. The analysis stage identifies the system components responsible for each vulnerability as well as its root cause.
Remediation
The final step in the vulnerability assessment process is to close any security gaps. This is usually a joint effort between the DevSecOps team, which sets out the most effective way to mitigate or remediate each vulnerability discovered. The remediation process includes introducing new cybersecurity measures, procedures, or tools; updating configuration and operational changes; and developing or implementing patches for identified vulnerabilities.
With the process completed, it is also vital for organizations to create a vulnerability assessment report. This needs to include recommendations on how to correct and mitigate vulnerabilities, risk mitigation techniques, and any gaps the assessment uncovers between the results and the organization’s system baseline.
The report needs to include the name of the vulnerabilities, the date they were discovered, and the score attributed based on the Common Vulnerabilities and Exposures (CVE) database. It also needs to include a detailed description of vulnerabilities, systems affected, processes required to correct vulnerabilities, and a proof of concept of the vulnerability.
Vulnerability Assessment Tools
Organizations can discover new and known vulnerabilities through specific vulnerability assessment tools. They should schedule regular and automated scans of their critical IT systems, and ensure the results of the scans are fed into their ongoing vulnerability assessment operation.
One of the most popular tools for vulnerability assessments is a web application scanner, such as the Fortinet Web Vulnerability Scanner. These tools scan, test, and simulate attack patterns of known vulnerabilities.
Protocol scanners can also be used to assess vulnerabilities. These are specifically designed to search for vulnerable network services, ports, and cybersecurity protocols. The other most common tool for vulnerability assessment purposes is a network scanner, which can be used to visualize organizations’ networks. It is also useful for discovering warning signs of vulnerabilities, such as insecure Internet Protocol (IP) addresses and spoofed or suspicious packet activity.
In addition, organizations should consider using plugins within the vulnerability assessment platform, such as scans of common and popular ports, firewalls, and content management systems (CMS), such as Drupal, Joomla, and WordPress.
How Fortinet Can Help: Vulnerability Assessment and WAF
Fortinet protects organizations and their business-critical applications through its FortiWeb web application firewall (WAF), which was named a Challenger in the 2020 Gartner Magic Quadrant for WAFs. Fortinet WAFs provide web applications with protection against attacks that target both known and new, or unknown, vulnerabilities.
The FortiWeb WAFs are particularly crucial to protecting organizations in the face of the ever-evolving threat landscape. Every time organizations deploy new web application features, update existing features, or expose new application programming interfaces (APIs), their attack surface expands. FortiWeb keeps pace with the expanding threat landscape, ensuring organizations are always protected through advanced features that defend them against known and zero-day threats.
FortiWeb uses an advanced and multi-layered approach that provides protection against high-risk threats, such as the Open Web Application Security Project (OWASP) Top 10. It also uses machine learning to customize protection for each application and ensure robust protection without the time-consuming manual modifications that other solutions require.
This enables the identification of anomalous, benign, and malicious behavior, as well as the capability to block malicious bot activity.
FortiWeb protects business applications wherever they are hosted, with options for hardware appliances, containers, cloud environments, Software-as-a-Service (SaaS) solutions, and virtual machines.
IBM Security Guardium Vulnerability Assessment
Сканирует среду данных в поисках уязвимостей и предлагает меры по их устранению
Выявляйте угрозы и слабые места в системе безопасности баз данных
Обнаружение конфиденциальных данных
Обнаружение конфиденциальных данных в гетерогенных средах и их классификация по уровню секретности.
Тестирование уязвимостей и создание отчетов
Создание подробных отчетов о предоставлении прав и об опасных конфигурациях.
Контроль за соблюдением стандартов
Автоматизация проверки соответствия нормам и стандартам и управление исключениями.
Основные возможности IBM Security Guardium Vulnerability Assessment
Изображения продукта
Security Assessment Builder
Готовые тесты для распространенных уязвимостей
Поддержка всех основных платформ баз данных
Настраиваемая административная сводная панель
Security Assessment Builder
Готовые тесты для распространенных уязвимостей
Поддержка всех основных платформ баз данных
Настраиваемая административная сводная панель